Learn how Application Performance Management as SaaS can do this all as a turn-key-solution.
Application Performance Management
Troubleshoot and monitor your code for greater efficiency, quicker releases and more satisfied customers. APM leverages the powerful data analysis platform in Elasticsearch to provide you with deep insights into your application’s operations and diagnose errors without waiting for a user to report them.
Fully managed, scalable, low-cost APM
Enable a scalable APM service without the burden of managing infrastructure or operating through another service(s). Trace your apps at any scale and get expert support on-demand to reach goals. Control costs through your data retention choices.
Not just an APM monitor tool
Connect your App traces with multiple dimension analytics leveraging aggregated logs and metrics, distributed tracing, machine learning capabilities, alerts, reporting, real user monitoring, service maps, and more. Profiling of services has never been more diverse.
Real User Monitoring (RUM)
Monitor real user experience and interaction within your client-side application in a framework-agnostic way. Troubleshoot proactively performance issues and JavaScript errors. Reduce the time to detect and resolve app incidents.
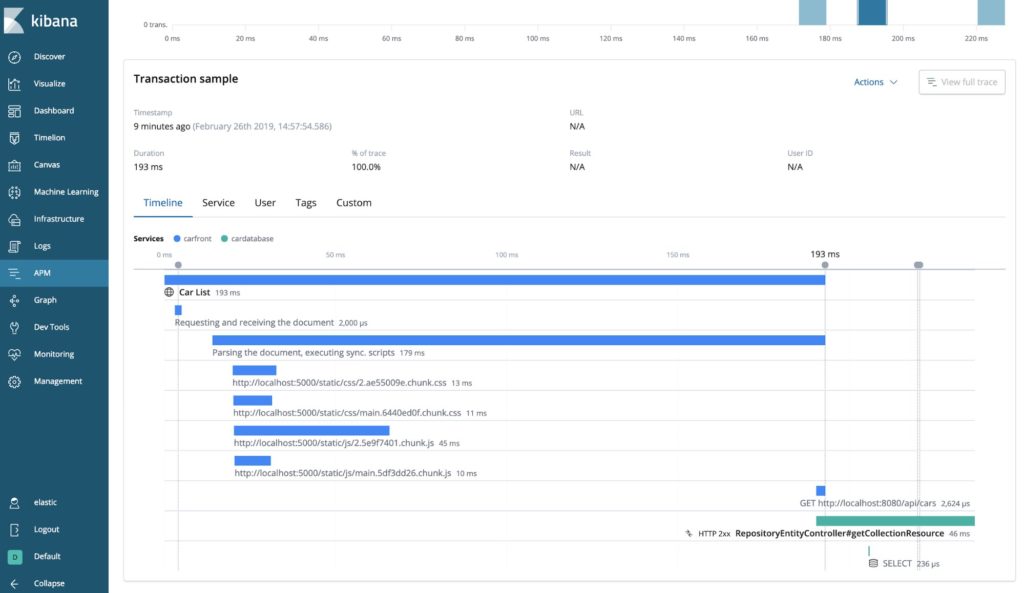
Built-in distributed tracing
See the whole picture of a single request throughout your complex system by tracing the entire chain of events, db queries, latencies, errors, and paths leading to bottlenecks. Eliminate service data silos, search, find, and fix issues faster.
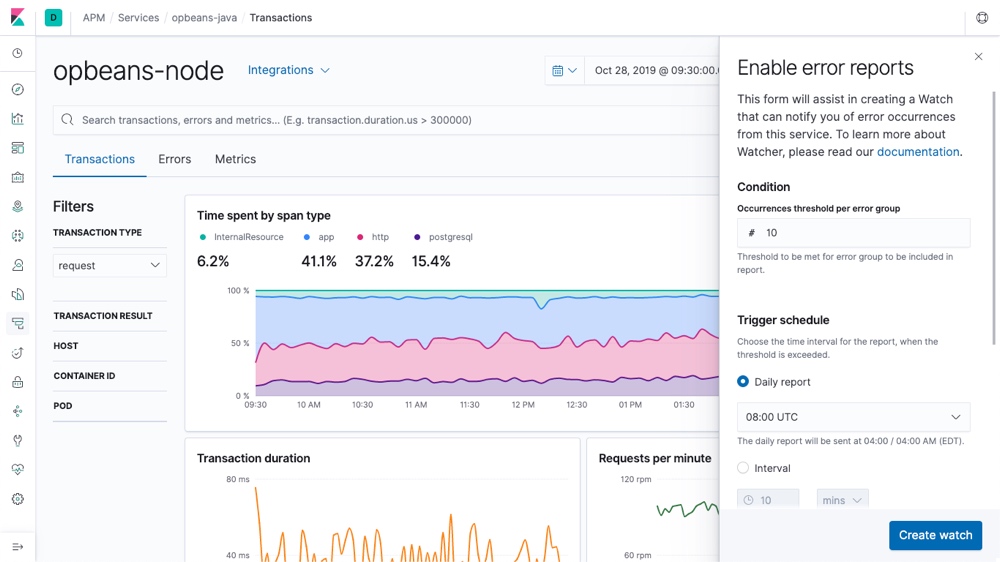
Alerts with actions
Create intelligent alerts and actions for the data context you are interested in. Get alerted via simple email for any communication or ticketing tool offering a REST api. Use role-based-access-control for alert rights. Trigger desired actions in the platform when conditions are met or connect to third-party systems to trigger a service process automation. Set conditions and triggers in a rich UI menu, with no code.
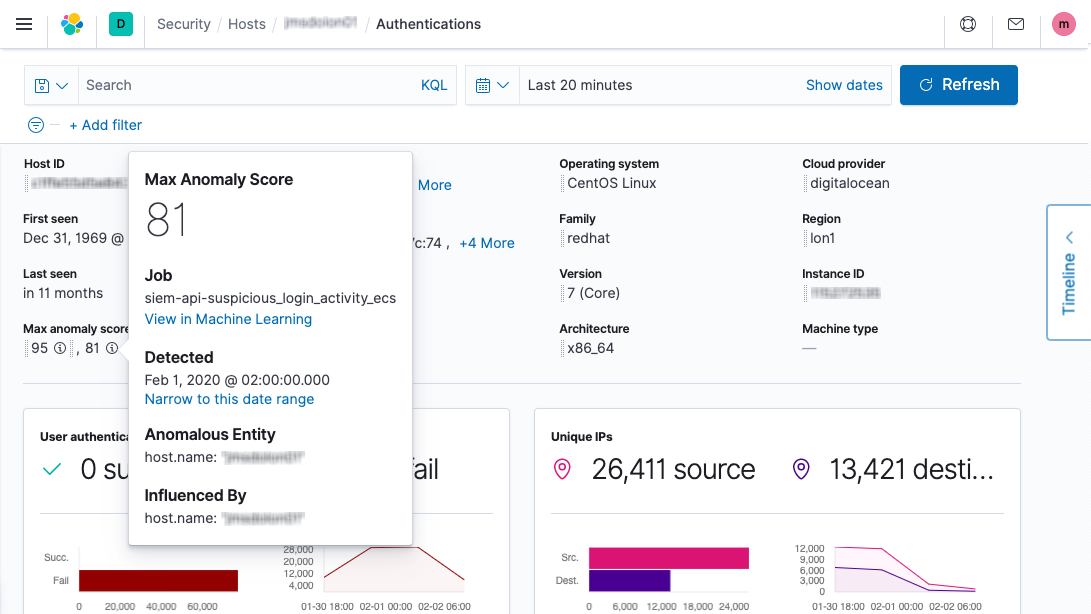
Respond proactively for anomalies
Ingest app traces, logs, metrics, correlate data, explore abnormal behaviours and issues with machine learning features that automatically model your data. Respond proactively to potential issues to avoid larger problems or SLA violations in production.
Industry leading APM security built-in
Integrate your app trace seamlessly with built-in SIEM security features and anomaly detection jobs. Identify requests from unknown scripts and requests to forbidden endpoints, detect unauthorized requests, and run queries for a specific attack.
Maximize your team productivity
Don't waste time scaling and maintaining your monitoring infrastructure. Focus on end-to-end visibility of your apps, follow the availability and performance of your SLA, gain a better customer experience with APM SaaS
Trace your App stack from anywhere
With service-included agents you can instrument the most popular programming stacks like PHP, Java, .NET, Go, Python, Ruby, and JavaScript seamlessly to APM at any scale.
In addition, you can leverage open standards such as Jaeger, OpenTracing or OpenTelemetry when sending data to APM analysis from your instrumented apps.
Get instant value with curated views delivered out of the box in SaaS, use all-encompassing search to discover your data, set repeatable queries, detect anomalies, fix issues faster, decrease complexity with holistic transparency.
No additional agent licenses, no data limits, no hardware, no complexity – just SaaS and on-demand expert support.

This is how it works
Easy as Pie
Easily instrumentize your applications with 4 lines of code. We support all major programming languages such as; Java, Go, Node.js, Python, Ruby, .NET, and Real User Monitoring (JavaScript). When setup you can see your application diagnosis at a glance.
APM lets you combine key metrics from apps with supporting services, datastores, and hosts, and optimize performance holistically in your operating environment. APM capabilities supports DevOps teams to collaborate, share, and work together to solve problems.
One tool to rule them all
We all know every deployment environment can be different. With APM easily compare the performance of different deployments, no matter where they are deployed. Find the root cause of performance bottlenecks with the Transactions view. Walk through a request from start to finish and zone in on the problem. Collect context and diagnostic information you need to fix your database performance issues such as response times for incoming requests and throughput, database queries, calls to caches, external requests.
Seeing is believing
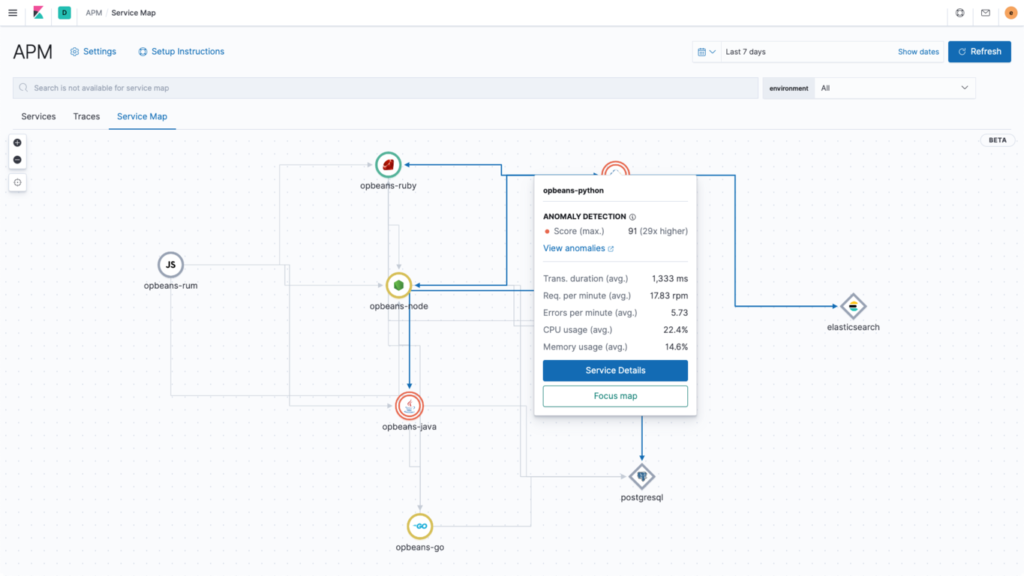
Visualize your stack like never before with service maps or multiple dashboards with a simple drag-drop interface, with any data you want – no coding needed.
See how your application is currently built to easily identify possible improvements. View how dependencies, modules, message queues, databases and your code all interact.
Enable alerts or custom policies to set up your own warning and critical thresholds staying on top of finding and resolving problems quickly.
Search for anything
At the core of APM is Elasticsearch, which means you get unparalleled search capacities to search and drill down into stack trace data.
Elastic’s inherent analysis of text means you will find what you’re looking for easily, no need to dig out the exact function names or source filenames.
Elasticsearch is used to store APM performance metrics and make use of its aggregations and provide real-time analytics.
Machine learning loves complexity
Nothing is too complicated. With Machine Learning (ML) models, even if your app is too complex to easily visualize, we can spot anomalies in the data and inform you about those outlier use cases that are causing problems, or specific code paths that are not performing well.
In addition, with combining built-in Elastic Security and ML detection capabilities, we can offer industry leading security detection by leveraging data collected from APM tracing, logs and metrics.
Any time, anywhere!
Continually monitor your apps in all production environments, including microservices, container clusters, or application integrations, and gain valuable insights to tune up your software and get alerted if problems occur.
Use Real User Monitoring (RUM) to capture user interaction with clients such as web browsers. RUM monitors the real user experience and interaction within your client-side application in a framework-agnostic way.
Or perhaps you would like to utilize OpenTelemetry or OpenTracing features? Ask for more about APM from our Elastic Engineers!
APM as SaaS
Sofecta as a Managed Service Provider (MSP) offers SaaS as a turn-key solution, including roll-out templates, product consultancy, security expertise, and maintenance. With SaaS we considerably save your time and costs in learning new technology, deploying it, keeping it maintained, updated, and hosted.
Get on board and take advantage of your Enterprise-level Elastic Stack features in days – we take care of engine and data ingest; you concentrate on analytics. The Elastic Stack as an 24/7 operated SaaS is available with full capabilities in audited, scalable and fault-tolerated environments. Ask for more from our sales!
Book your free demo with our colleagues from our customer success team to find out how much you can benefit from moving to the Sofecta APM SaaS today!
Further reading
Did you know that our Application Performance Management SaaS works seamlessly with our other solutions as well? Why not have a further read on one of the topics below or visit our blog!
SIEM as a Service
Enable cost-effective anomaly detection and threat hunting with intuitive Elastic Security SIEM as a Service, and establish a holistic view to information across your cloud environments.
Learn more

Container Orchestration
Accelerate the development of your business services, streamline operational capability, deploy workloads at the Edge or hybrid mode, and achieve superior security in your environments.
Learn more

Security Consultants, Analysts and Researchers
Take advantage of our experienced Managed Detection and Response (MDR) specialist consultants to mitigate the security threats and vulnerability risks in your business.
Learn more